More Innovation:
Cyphercor’s LoginTC Adds a New Dimension to VPN Security
New to the CENGN community, and eager to deploy their innovative solution on the CENGN Testbed, is Cyphercor from Kanata, ON.
Cyphercor has developed a security solution for stronger authentication of users. Their adaptive, two-factor authentication product, entitled LoginTC, adds another dimension of security to an organization to keep the bad people out, while keeping it simple for the good ones to log in. LoginTC protects an organization’s VPNs, websites, ERPs and networks, and appeals to businesses and organizations of all sizes, and all sectors (eg, Government, finance, IT, health care).
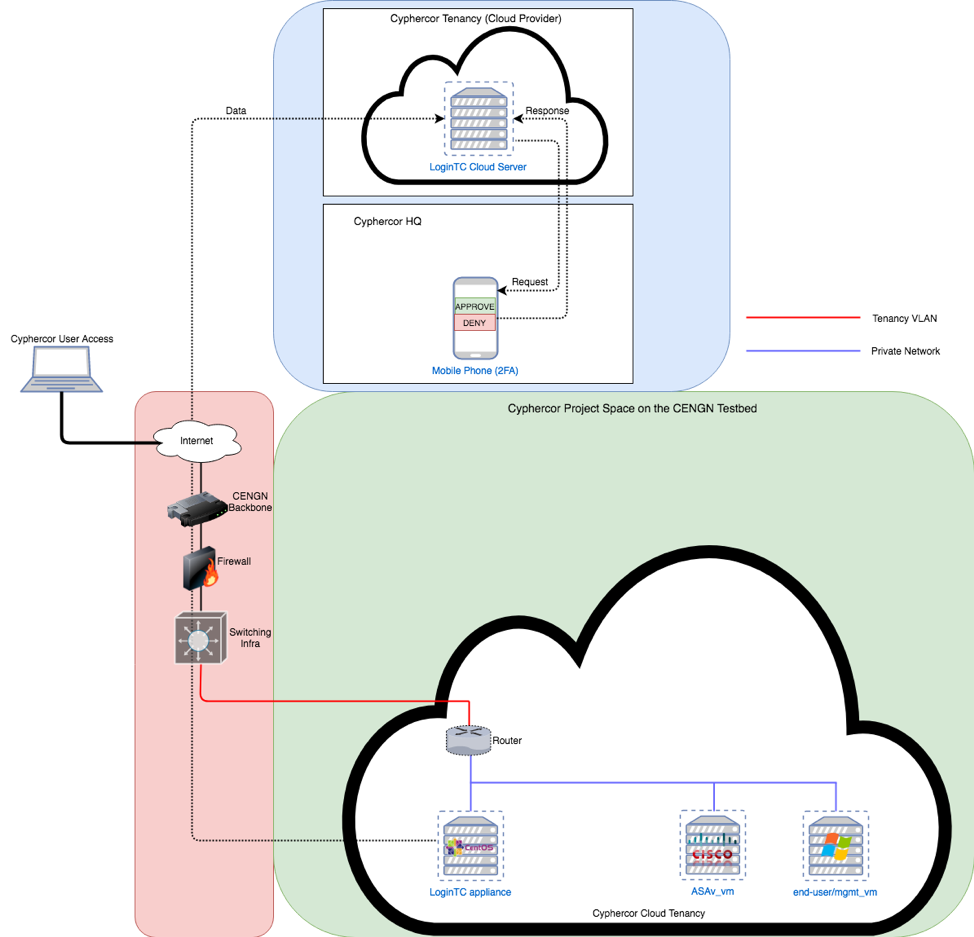
Cyphercor came to CENGN to utilize both our infrastructure services and our business connections as they will be using a VPN from one of our long-time tier 1 members, Cisco. In this security project, Cyphercor will be testing the integration and functionality of LoginTC with Cisco’s ASAv (Adaptive Security Virtual Appliance), as well as showcasing the solutions unique security features.
The Story Behind Cyphercor
The team at Cyphercor embraces a high-profile resume as their leadership team has held positions in companies such as Microsoft, Bell Canada, Nortel, Tropic Networks (acquired by Alcatel-Lucent), PostRank (acquired by Google), and Hulu. Noticing story after story in the news about cyber-attacks and password breaches, Cyphercor’s Founder, Diego Matute, decided to create a solution that was different from the others. The company decided to create a cybersecurity product that focused on three areas: cost effectiveness, usability, and security that goes beyond modern day standards. No matter the industry sector, every company needs to take stronger measures to protect their proprietary information and customer data. The fact is, today’s security measures are not keeping up with the level of efficiency seen by hackers and cyber-attacks.
For a start-up, Cyphercor has had some pretty large clients adopt their solution, most notably the Federal Government of Canada. In December 2016, Cyphercor was awarded a contract with the Canadian Government through the Build in Canada Innovation Program (BCIP). Cyphercor’s LoginTC integrated seamlessly with one federal government agency’s IT infrastructure systems due to its ease of use, quality of security, and ability to integrate adaptive two-factor authentication on top of the agency’s existing systems. The solution has been subsequently deployed into production by other departments and even more departments and agencies are investigating its potential.
Not only has the Federal Government of Canada trusted Cyphercor to protect their solution, business and organizations dealing with sensitive data, around the world, LoginTC customers include:
– USA-based counties and city governments
– Electric utilities
– Mortgage, financial planners, investment and law firms
– European food producers
– Canadian auto industry suppliers
– And dozens of IT reseller, support and consulting firms
Cyphercor’s growth has been truly remarkable over the past few years, and it is for good reason that the company’s LoginTC security solution is being adopted across markets. So, before we dive into the CENGN project to come, let’s take a look at how LoginTC is changing the cybersecurity game for businesses across Canada.
How LoginTC is Advancing the Security Industry
Most modern security measures rely solely on knowledge-based authentication. Knowledge authentication is dependent on a user’s personal information and can include logging in through passwords, answering security questions, or even identifying Facebook friends in a photograph. Unfortunately, knowledge-based authentication has been proven over and over again to be unreliable. Let’s say a hacker has gained access to your password (… and this often occurs due to sloppy password habits). A little research into your past can easily provide them with the correct answer to a security question, thus providing access to your account. For this reason, Cyphercor has sought another dimension of authentication to the login process that goes beyond knowledge-based elements.
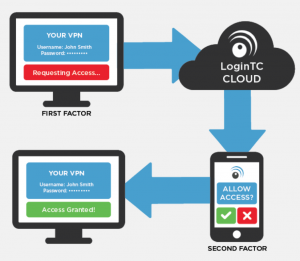
Cyphercor’s LoginTC augments knowledge-based elements (known as “first” factors) by adding a requirement for a second factor to complete an authentication. The second factor is the possession of a device; specifically, a smartphone. The second-factor authentication is completed through an approve or deny “push” notification sent to the user’s smartphone.
Here’s how it works:
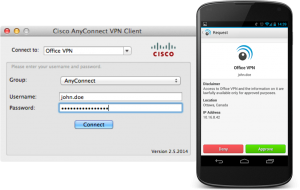
The user begins the access login process (to a VPN, network, or web site) by inputting their username and password into their PC, laptop, or other user interface. Upon successful passing of their first factors, the LoginTC cloud server sends a notification, via the “push” capabilities of the Google, Apple and Blackberry networks, to the user’s own smartphone. From the notification on the smartphone, the account holder can see the contextual information on their own login attempt; for example, location and IP address. Thus, ensuring that it is themselves attempting to access the IT resource; not a hacker or outside actor. They can now select whether to Approve or Deny it. By tying a successful login process to another device, Cyphercor has added a new dimension of protection. Now a hacker would need to both know the login password and have the user’s phone in their possession to gain access to the account.
On top of two-factor authentication, LoginTC leverages adaptive authentication. Adaptive authentication adds flexibility to the security measures taken when a user logs in. This can be used to add security when a login attempt seems abnormal to a user’s past behavior and therefore more likely to be a hacking attempt. For example, LoginTC can use geo-velocity to enact additional authentication measures based on time and location. So, if you login in Ottawa and 5 minutes later a login is attempted in Vancouver, the system is aware that it’s humanly impossible to travel from Ottawa to Vancouver that fast and can add heavier login security measures.
Testing the Functionality of Adaptive Authentication
Completing a project on the CENGN Testbed will benefit Cyphercor’s LoginTC in two ways. First, the project will validate the functionality of LoginTC with Cisco’s ASAv. Successful integration of LoginTC with Cisco’s ASAv will prove the compatibility of their solution and add another virtual appliance to Cyphercor’s growing list of VPN Connectors. The second goal of the project is to test the adaptive authentication feature of LoginTC. This will further enhance and validate LoginTC’s ability to run real-time heuristics and step-up security measures based on a dynamic policy rules engine.
Cyphercor’s LoginTC is a great example of the versatility of CENGN’s services. Not only are we available to help early stage companies accelerate the commercialization process of their solution as they move from R&D to market, we can also help small and medium enterprises (SMEs) with established solutions. LoginTC is currently available on the market but testing an additional feature of their product will help them not only serve their customers better but differentiate their services from their competitors.
Beyond cybersecurity, CENGN works with growing Canadian businesses to validate next-generation networking solutions in SDN/NFV/SD-WAN, Internet of Things, data centre and cloud, mobile networks, network transport, and network applications.









